BlueGreen Water Technologies Ltd. Names Jurgens Van Loggerenberg Africa Head Of Operations
BlueGreen, a global cleantech company, announced today that it has named Jurgens Van Loggerenberg as its Africa Head of Operations….
BlueGreen, a global cleantech company, announced today that it has named Jurgens Van Loggerenberg as its Africa Head of Operations….

I have been keen on what’s happening in Kenya’s tech scene, in particular digital transformation initiatives centred around making life…

The Franklin Templeton Emerging Markets Equity team examines the impact of the spread of coronavirus across emerging market economies during…

East Africa has not been a beneficiary of African Private Equity (PE). In fact, according to a 2020 Preqin…

The database management systems are presently expanding and coming up with new features! Today, several database platforms cater to Big…

An information security policy is the foundation of an enterprise security program, ideally establishing in clear language what the organization…
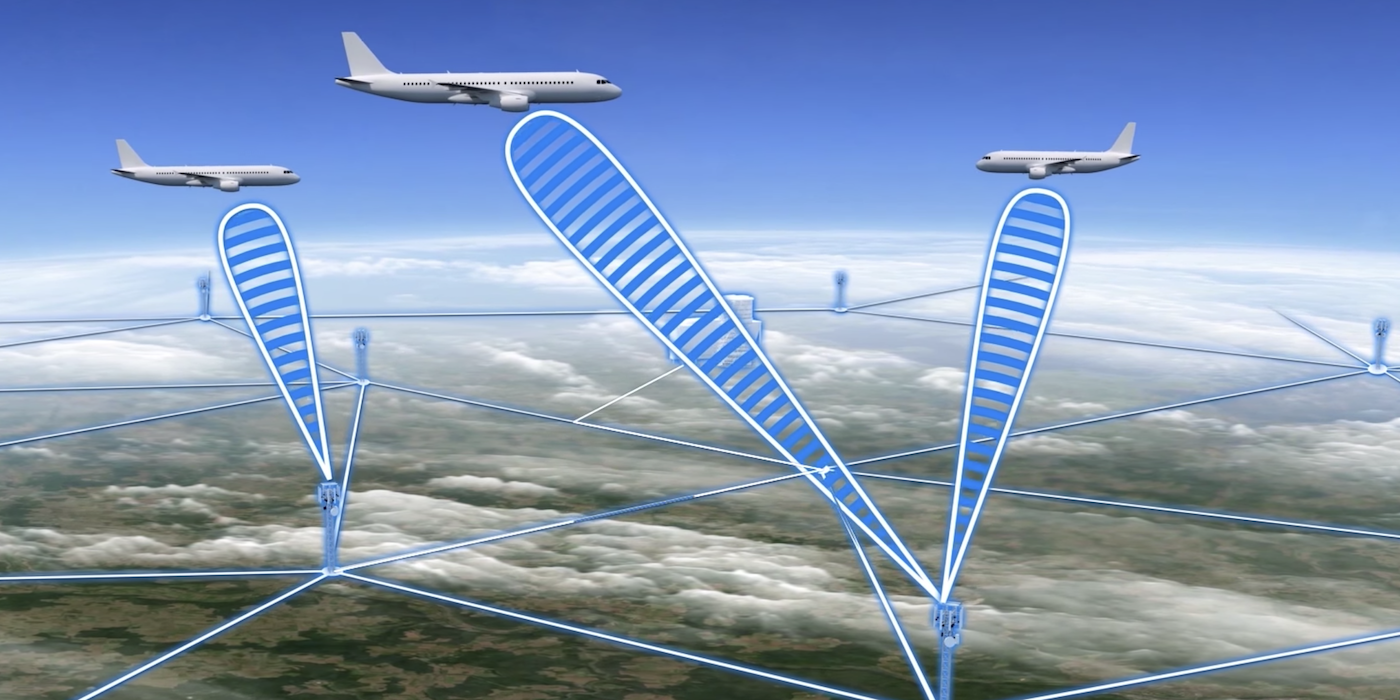
SITA, the leading IT provider for the air transport industry, has made six predictions about how ultra-fast 5G networks will…

African telco operators face a landmark five-year period as they strive to reimagine their business models and build new capabilities…

Research shows far-reaching impact of Pay on Demand model, with users and their families living happier and healthier lives,…
With 5G poised to become widely available across the globe, enterprise organizations need to seriously consider the security implications of…
No more posts available. Thank you for scrolling this far.
No more posts available. Thank you for scrolling this far.