7 Ways To Harden Your Environment Against Compromise
Here at the global Microsoft Compromise Recovery Security Practice (CRSP), we work with customers who have experienced disruptive security incidents…

Here at the global Microsoft Compromise Recovery Security Practice (CRSP), we work with customers who have experienced disruptive security incidents…

When you think of manufacturing, you picture a large and grimy factory, with rows and rows of individuals, doing menial…

Asset disposal normally isn’t one of those burning topics that is top-of-mind for CISOs, yet every CISO must be able…

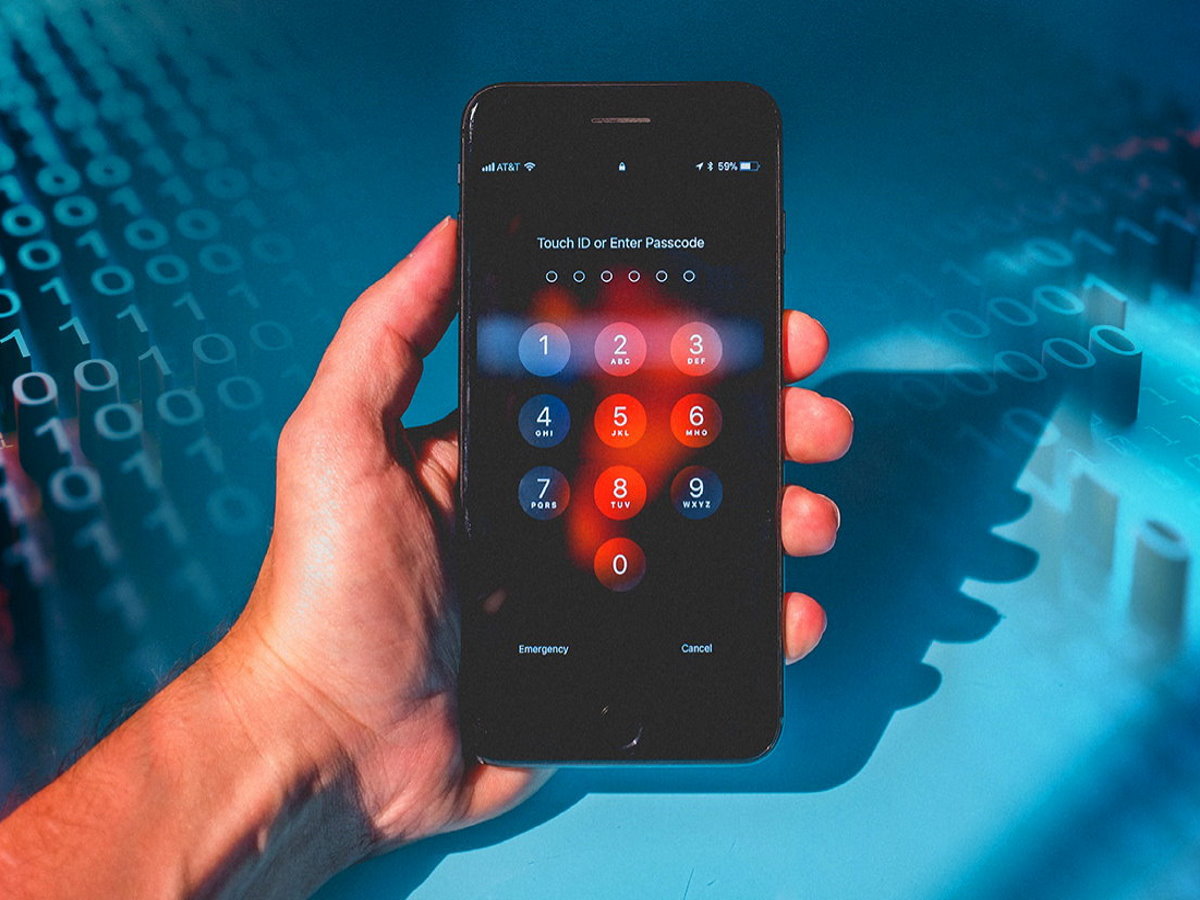
What is credential stuffing? Credential stuffing is the automated use of collected usernames and passwords to gain fraudulent access to…
With Kaspersky research showing that stalkerware affected one out of every 100 mobile users in Kenya and Nigeria in 2020…

In the last few years there have been a number of phrases and key words that have been floating around…

As the buzz continues on the use and adoption of IoT in all sectors of the economy, so are the…

The government of Rwanda has over the last five years aggressively pursued and invested heavily in the information and communications…

On 28th and 29th March, CIO East Africa and Rwanda Information Sociecty Authority (RISA) will host Cloud and Security Summit…

With a new hacking scandal in the news every other week, everyone should be concerned about the security of their…
No more posts available. Thank you for scrolling this far.
No more posts available. Thank you for scrolling this far.