Axiz tops at the ChannelWatch Distributor of the Year Award
Leading local value-added ICT distributor, Axiz, has cleaned up at the 2019 CONTEXT ChannelWatch Awards, winning in three categories –…
Stay up-to-date with the latest developments in cybersecurity on our website. From data breaches to cyber threats, we cover the latest news and insights on how to keep your organization secure. Discover best practices for protecting your systems and data from cyber attacks, and gain insights into emerging technologies like artificial intelligence and machine learning.
Leading local value-added ICT distributor, Axiz, has cleaned up at the 2019 CONTEXT ChannelWatch Awards, winning in three categories –…

Kaspersky recently conducted an overview of smart building threats and reported that almost two in ten (26.5%) computers used to…
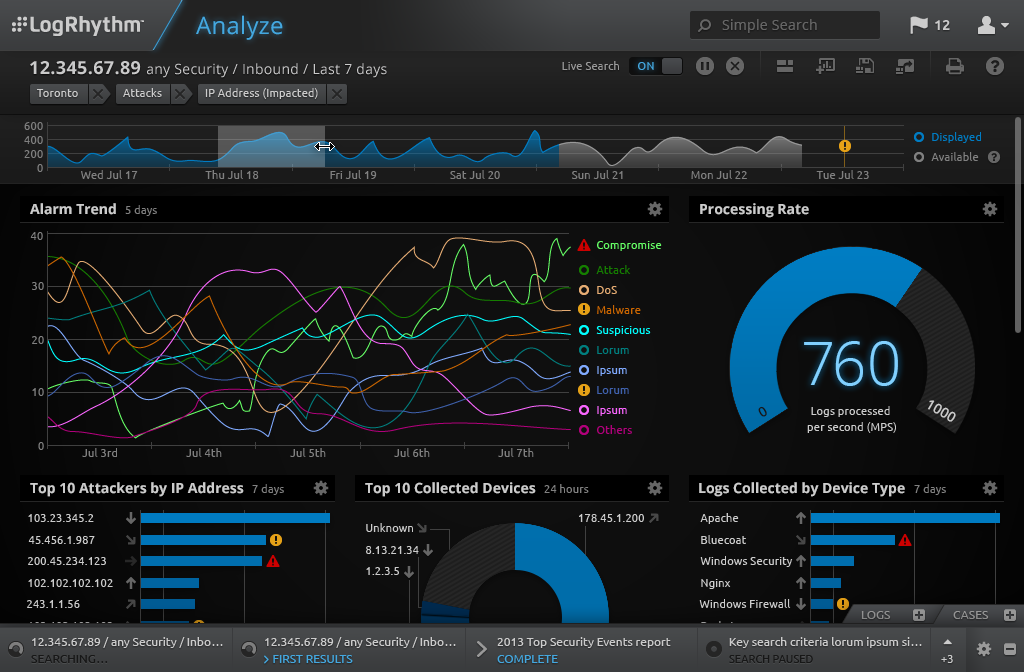
Historically, organisations have paid more as data ingestion increased. While others in the industry have previously claimed to support unlimited…

ThreatQuotient has announced that it shall be making its first appearance at GITEX Technology Week this year. A believer in threat…

A value-added technology distributor, Westcon-Comstor, has been appointed as a Check Point distributor for the Sub-Saharan African region. The appointment…

Trend Micro has been cited as a leader with the second-highest score in the current offering category in The Forrester…

There is a misplaced confidence in existing cybersecurity solutions and the beleaguered IT department that is leaving corporate doors wide…

When it is globally appreciated that there is a shortage for trained cybersecurity professionals, Kenya only has about 1600 trained…

Africa’s Fintech sector is booming! According to reports, Africa’s Fintech ecosystem has surged 60% in the last two years and the…
By Ali Raza, Head Business Development US Region Globally e-commerce is booming. According to industry estimates digital commerce is projected…
No more posts available. Thank you for scrolling this far.
No more posts available. Thank you for scrolling this far.