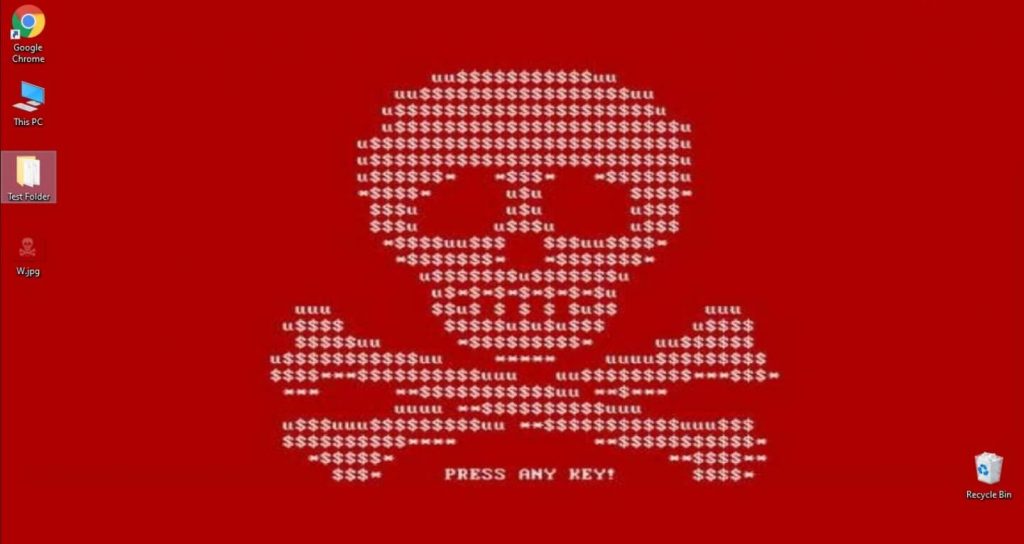
DearCry Attacks Microsoft Exchange Server Vulnerabilities
After the Microsoft Exchange vulnerabilities were reported and the out-of-band release of security patches on 2 March, security researchers started…
Stay up-to-date with the latest developments in cybersecurity on our website. From data breaches to cyber threats, we cover the latest news and insights on how to keep your organization secure. Discover best practices for protecting your systems and data from cyber attacks, and gain insights into emerging technologies like artificial intelligence and machine learning.

After the Microsoft Exchange vulnerabilities were reported and the out-of-band release of security patches on 2 March, security researchers started…

Checkpoint together with her partner DGIT has penned a sponsorship deal towards the forthcoming East Africa Cloud and Cybersecurity Summit…

Sophos has uncovered how attack code behaves while hiding in memory and built protection against it in a discovery bid…

Following Microsoft news on Hafnium, Sophos has been closely monitoring the issue and is providing regular advice on how organizations…
Kaspersky researchers have identified a new, previously unknown, campaign from Lazarus, a highly prolific advanced threat actor active since at…

Check Point, a provider of cybersecurity solutions globally, has extended the capabilities of its unified CloudGuard Cloud-Native Security platform with…

Sophos researchers have in a three-part series of articles, unveiled what happens when attackers break into an organisation’s network with…

The Communications Authority of Kenya (CA) has, in partnership with local telecommunications service providers, launched an interactive portal aimed at…

Tuesday 9 February marks the day the world celebrates safety on the net, or Safer Internet Day if you like….

Kaspersky has joined forces with Waterfall Security Solutions to better secure industrial networks. Kaspersky Industrial CyberSecurity for Networks in tandem…
No more posts available. Thank you for scrolling this far.
No more posts available. Thank you for scrolling this far.