Google may charge you for user data requests
Google may soon start billing government and law enforcement agencies for legal demands seeking user data requests such as emails,…
Discover the latest news and insights in the exciting world of the Internet of Things (IoT) on our website. We cover everything from connected devices and smart homes to industrial IoT and the impact of IoT on society. Stay up-to-date with the latest developments in this rapidly-evolving field and gain insights into how IoT is transforming the way we live and work.

Google may soon start billing government and law enforcement agencies for legal demands seeking user data requests such as emails,…

Cryptojacking is the unauthorized use of someone else’s computer to mine cryptocurrency. Hackers do this by either getting the victim…

Liquid Telecom is set to launch the first 5G wholesale roaming service in South Africa to allow businesses harness new…

Even in the high-touch field of healthcare, where human interactions remain core to the delivery of most services, IT exec…
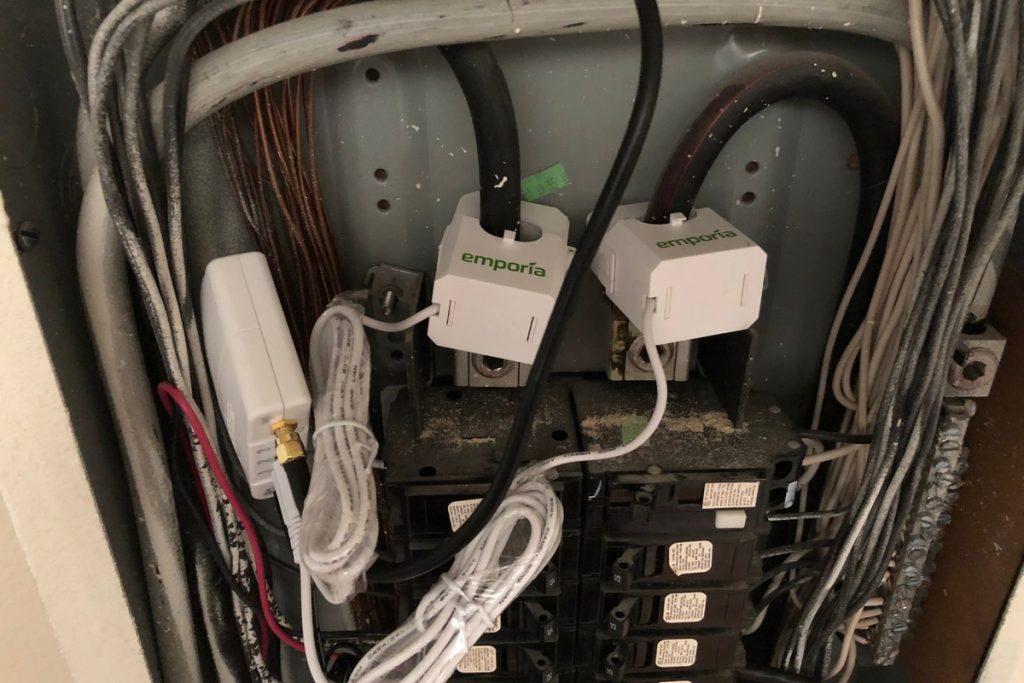
Even novices can use this system to easily get a grip on how much juice they’re using Want to know…

Imagine what you would have done differently in your network if you could have just seen a few years into…

Central banks in Asia and Europe are in the final stages of launching digital currencies for future payment systems and…

Three-quarters of companies implementing IoT have already adopted blockchain or plan to use it by the end of 2020, an…

Friday 20th December 2019 marked a major landmark achievement for Africa, when Ethiopia launched its first satellite into space, making…

The internet is 50 years old, long live! Most of us probably come from a time when the internet is…
No more posts available. Thank you for scrolling this far.
No more posts available. Thank you for scrolling this far.