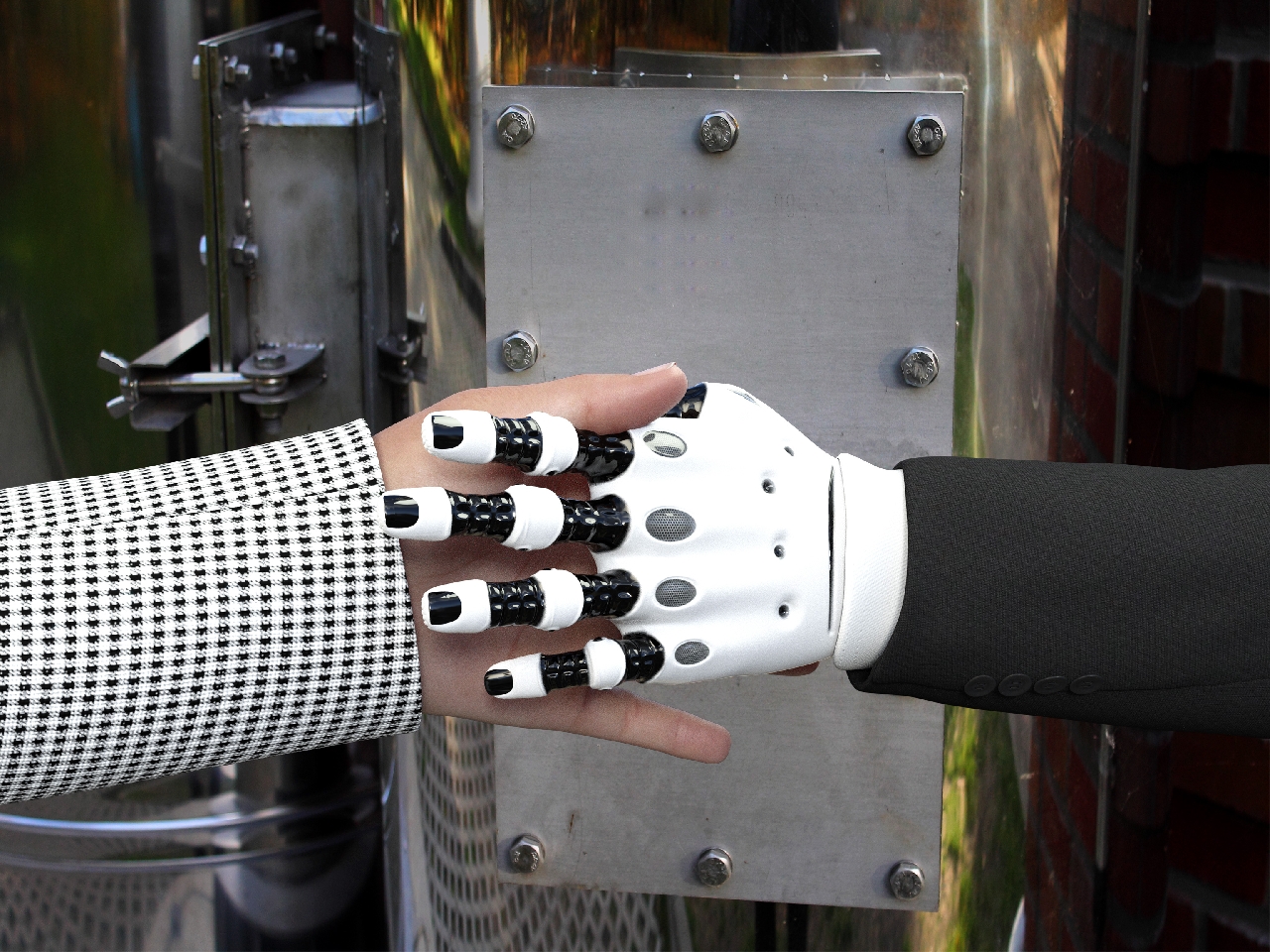
Delivering A Collaborative Cybersecurity Services Model For Telcos And Systems Integrators
With the new year well underway, it has quickly become apparent that the intensification of the cyberthreat landscape that the…

With the new year well underway, it has quickly become apparent that the intensification of the cyberthreat landscape that the…

Google is buying cybersecurity firm Mandiant for $5.4 billion as part of its plan to protect its cloud customers better….

Cisco East Africa Regional Manager and Country Manager, Kenya, Sally Kimeu outlined four things CIOs must be able to do…

Cybersecurity, digital transformation, cloud computing and retaining IT talent are among the top priorities for CIOs this year. The revelations…

This year will see an increase in phishing attacks compared to other forms of attacks, Down To Earth (DTE) Technologies…
Pushing The Limits: How To Address Specific Cybersecurity Demands And Protect IoT, a Kaspersky study, revealed two-in-five businesses (44 per…

As cybersecurity professionals, we need to be diligent about doing everything we can to increase our chances of success. Any…

Check Point Technologies, a leading provider of cybersecurity solutions globally, has partnered with the Namibia University of Technology (NUST), Complete…

Cybersecurity is about what you can do — not what you can’t do. The threat landscape is expanding. Cybercriminals are…

What would you imagine your username and password are worth to a hacker? According to Microsoft’s latest threat and data…
No more posts available. Thank you for scrolling this far.
No more posts available. Thank you for scrolling this far.