LG launches user-centric devices to transform security at home
LG has introduced user-centric devices, the LG Hub robot that will provide home security solutions. The device which features motion…
Stay ahead of the curve on the latest cybersecurity news and trends with our expertly curated collection. Our collection offers diverse perspectives and insights from industry experts and thought leaders to help you stay informed and protected against emerging threats. Discover the latest trends in cybersecurity, including artificial intelligence, machine learning, cloud security, and more. Our curated collection brings together news articles and analysis from multiple sources to provide you with a comprehensive overview of the cybersecurity landscape. Whether you’re an IT professional, a business owner, or simply interested in staying informed about cybersecurity trends, our curated collection has you covered. Protect yourself and your business by exploring our comprehensive cybersecurity news and trends collection today.

LG has introduced user-centric devices, the LG Hub robot that will provide home security solutions. The device which features motion…

Just because Windows 7 is close to eight years old doesn’t mean you still can’t find ridiculous bugs that can…

According to a 2016 study from IBM regarding the costs of data breaches and loss, the average consolidated cost moved…
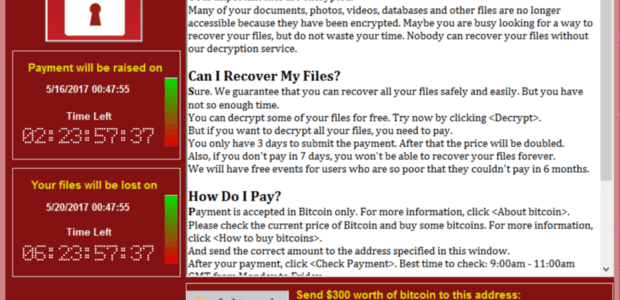
The WannaCry exploit was global news, but it seems to have died down. Is the worst over, or is this…

The Communication Authority of Kenya (CA) through the National Kenya Computer Incident Responce Team (National KE-CIRT) anounced on Friday that…

afaricom has opened its 45th shop in Kitengela town and unveiled its Nairobi East Regional Office as part of its…


If you own a Windows XP or Windows 7 PC that’s been hit by the WannaCry ransomware, there’s good news:…
ransporters are facing more challenges now more than ever before – from increased regulation, push towards harmonization, security and privacy…

Joe Mucheru, Cabinet Secretary in the Ministry of Information and Communication Technology Joe Mucheru, Cabinet Secretary in the Ministry of…
No more posts available. Thank you for scrolling this far.
No more posts available. Thank you for scrolling this far.