Open Source Initiative, Breathing Games collaborate by creating open source gaming software
With one person in five now affected by chronic respiratory diseases-asthma, obstructive disease, and cystic fibrosis among many others-creating effective…
Stay informed with the latest technology news from around the world with our curated collection of articles. Our comprehensive coverage includes news on emerging technologies, advancements in science and engineering, and the impact of technology on society. Discover a range of perspectives from our global network of contributors, offering insights and analysis on the most pressing issues in tech today. Explore our collection to stay up-to-date on the latest trends and developments in technology from around the world.

With one person in five now affected by chronic respiratory diseases-asthma, obstructive disease, and cystic fibrosis among many others-creating effective…
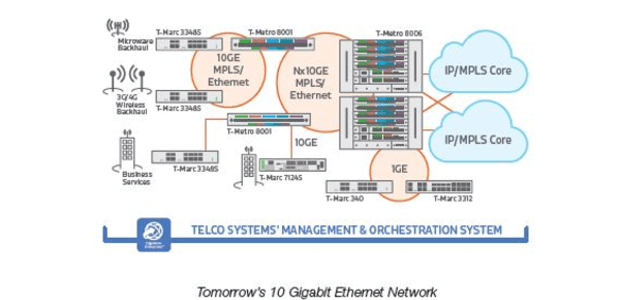
Telco Systems announced that it has successfully deployed a new 10GE high capacity carrier Ethernet network for the Kenya Education…

SAP has partnered with waste management expert PROLOGA, to address many of the challenges around this industry: from route planning,…

Aleda has been Orange’s long-standing wholesale partner for the distribution of pre-paid telephone offers but with the collaboration Aleda provides…

Acer, a Taiwanese Company, has revealed to California’s Attorney General (AG) that hackers broke into the company’s online store and…

Following the successful resolution of the Nigerian dispute, MTN Group has completed the review of its governance and management structures…

The outcome of the review process is expected to be a comprehensive policy document that is aligned with the new…

25% of the respondents had been directly involved with a network built using money from USF and were extremely well-informed…

Robert will use the funds to link girls to health and legal experts who will provide answers to their questions…

The Chan Zuckerberg Initiative is leading a new $24 million Series B round of funding into Andela, the first lead…
No more posts available. Thank you for scrolling this far.
No more posts available. Thank you for scrolling this far.