Why Colocation Is Right For Your Business
You may be wondering, what really is data center colocation? Well, co-located data centers are enterprise grade data centers with…
Blogs on tech trends, products, services and technologies, including cloud computing, security, artificial intelligence and more

You may be wondering, what really is data center colocation? Well, co-located data centers are enterprise grade data centers with…

A passenger on a Singapore Airlines flight noticed a small, circular indentation below the image playing on the seatback in-flight entertainment…

When we launched rAINbow, an artificial intelligence-powered smart companion that aims to democratise support for victims of domestic violence, in…
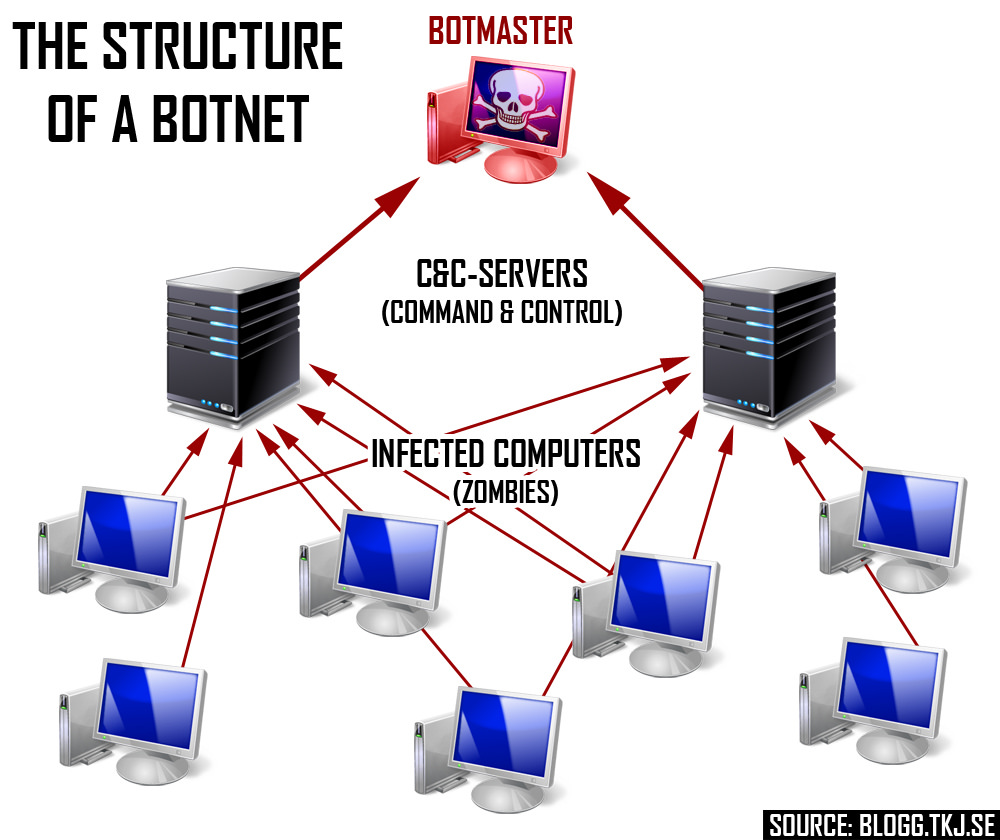
A botnet is a collection of any type of internet-connected device that an attacker has compromised. Botnets act as a…

The role of cloud as an IT and business tool is now more than a decade old. Globally, IT departments…

A few days before writing this article I had received a call from a client who was looking to fill…
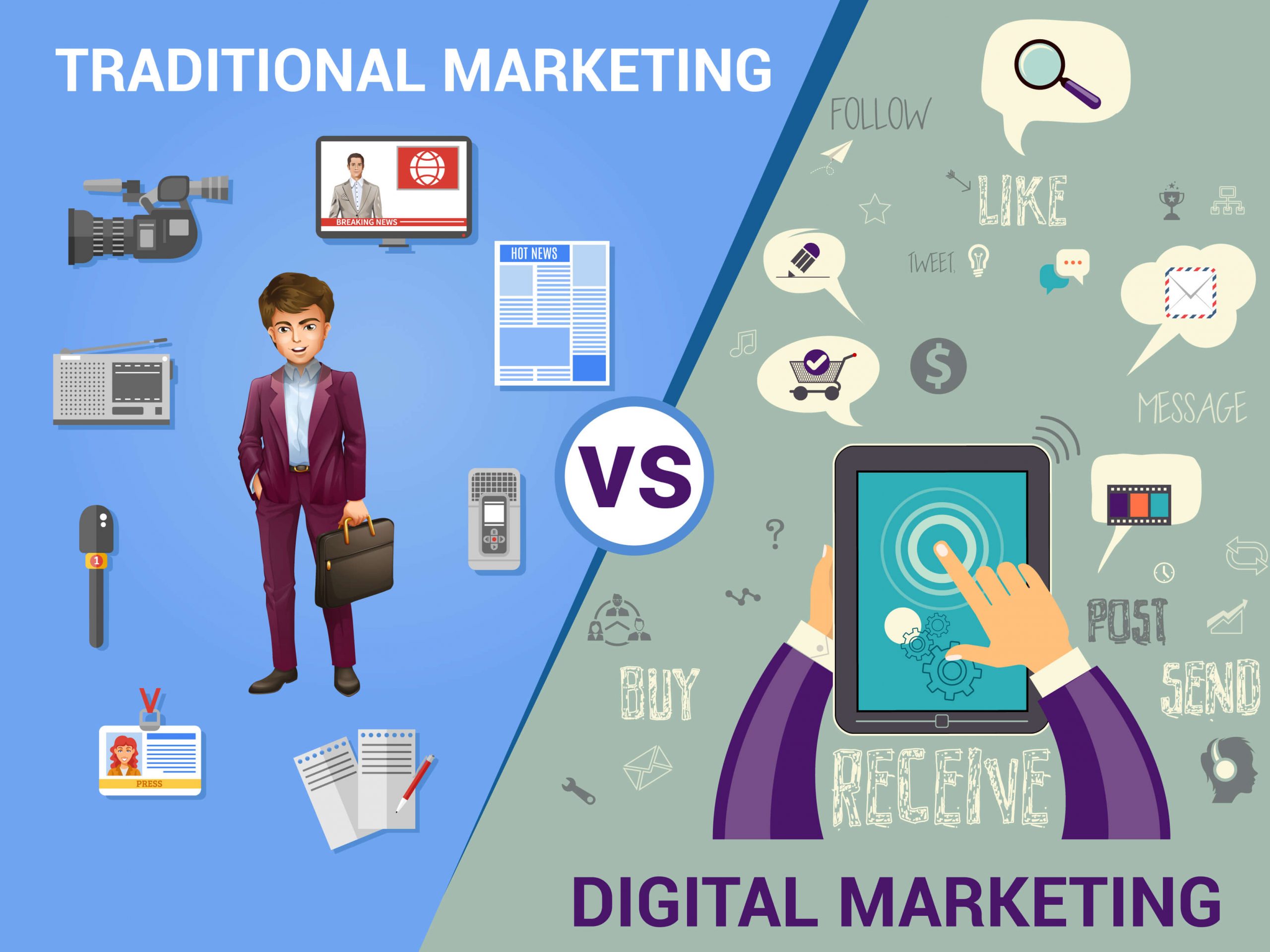
The most successful marketing campaigns use a mix of digital and traditional marketing. A digital marketing approach may work for…

The British parliamentarians were mad recently because the co-founder of Facebook decided to send an emissary to explain to them…

Between 1887 and 1889 the definition of theft changed as man learned to replicate things in a rapid form, this…

On 12th December 2017, Uhuru Kenyatta, Kenya’s President shared the agenda for his government’s next five years. Fortunately, it did…
No more posts available. Thank you for scrolling this far.
No more posts available. Thank you for scrolling this far.