7 mobile security threats to take seriously in 2019
Mobile security is at the top of every company’s worry list these days — and for good reason: Nearly all…
Stay up-to-date with the latest developments in cybersecurity on our website. From data breaches to cyber threats, we cover the latest news and insights on how to keep your organization secure. Discover best practices for protecting your systems and data from cyber attacks, and gain insights into emerging technologies like artificial intelligence and machine learning.

Mobile security is at the top of every company’s worry list these days — and for good reason: Nearly all…

The advancement in technology and faster internet penetration has made things easier and convenient for businesses and individuals alike but…

Whether you’re buying things online, posting on social media or just reading your emails, there are potential traps at every…

Is your vision 2020? Or maybe 2030? Are you planning your strategy now based on what may happen over the…

The National Information Technology Authority – Uganda (NITA-U) in alliance with the Internet Corporation for Assigned Names and Numbers (ICANN)…

As drones continue to permeate ever more sectors of the Kenyan society, the question about the potentiality of using them…
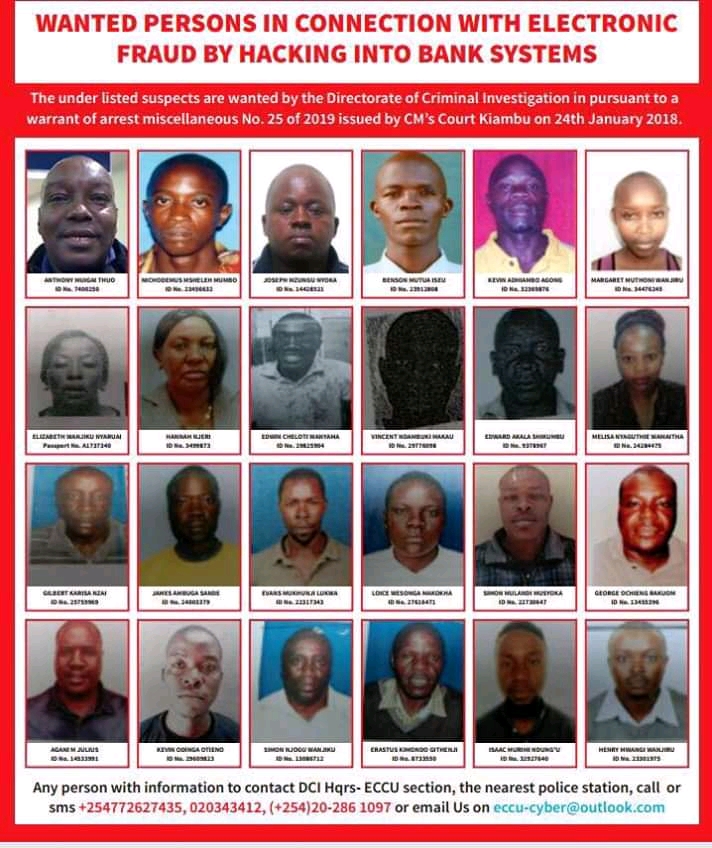
The Directorate of Criminal Investigations (DCI) on Wednesday the 30th January 2019, published names and images of 130 suspects implicated…

A supply chain attack, also called a value-chain or third-party attack, occurs when someone infiltrates your system through an outside…

The C-suite and boards of directors often think about investment decisions under three key pillars – Will this decision make…

Instead of using mass spamming techniques to blast malware to millions of recipients in the hope of collecting thousands of…
No more posts available. Thank you for scrolling this far.
No more posts available. Thank you for scrolling this far.