Why Managed Security is the way to go for modern Businesses
In the last few years there have been a number of phrases and key words that have been floating around…
Stay up-to-date with the latest developments in cybersecurity on our website. From data breaches to cyber threats, we cover the latest news and insights on how to keep your organization secure. Discover best practices for protecting your systems and data from cyber attacks, and gain insights into emerging technologies like artificial intelligence and machine learning.

In the last few years there have been a number of phrases and key words that have been floating around…
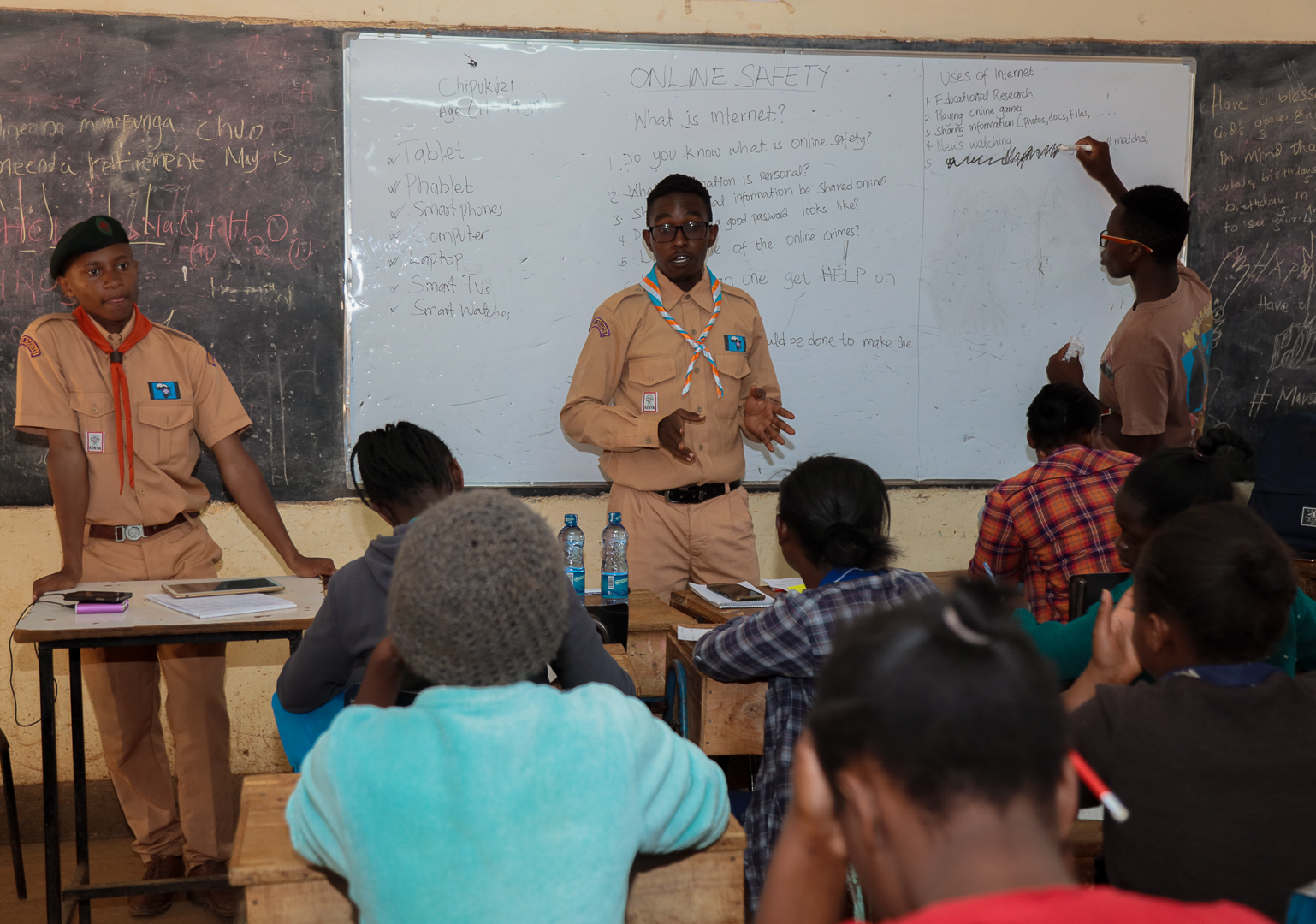
A Kenyan based NGO together with the Kenya Web Rangers have extended their online safety training to youth in Karuri…

Data was said to be the new oil that, bad as it sounds, can be used and/ or misused in…
The world recently experienced an outage from Google that affected Gmail and Google Drive services inhibiting the access of google…

Both “low and slow” approach to financially driven cyber attacks has overtaken ransomware as the chief attack vector for criminals…

With barely a fortnight to the East Africa Cloud and Security Summit (CSS) curated by Rwanda Information Society Authority (RISA)…

It is becoming increasingly difficult to keep r valuable data under control. As data users continue to acquire more credentials…

Serianu purposed to remain on the forefront in warring against cybercrime in Africa; partly owing to unprecedented voluminous loses experienced…

Any organization’s staff members continue to be a weakest link of operations since they harbor information that help grow the…

Although a Virtual Private Network (VPN) encrypts connections to the internet to give online privacy and anonymity, security has somewhat…
No more posts available. Thank you for scrolling this far.
No more posts available. Thank you for scrolling this far.