How Educators Can Help Stem The Tide Of Cyber-bullying
It’s perhaps one of the great paradoxes of our time – the opportunities that technology presents come with complexities that…
Stay up-to-date with the latest developments in cybersecurity on our website. From data breaches to cyber threats, we cover the latest news and insights on how to keep your organization secure. Discover best practices for protecting your systems and data from cyber attacks, and gain insights into emerging technologies like artificial intelligence and machine learning.

It’s perhaps one of the great paradoxes of our time – the opportunities that technology presents come with complexities that…

Sophos has published a SophosLabs report, Don’t Let Fleecewear Sneak into Your iPhone showing how Apple device users are being…

We all know that finding talented cybersecurity professionals is not easy. Making matters worse, neither is keeping them. According to ISACA’s…

What lessons can be learned from reviewing how we manage cybersecurity and applying it to an anti-Coronavirus campaign? In…

As part of its adoption and implementation of the Cybersecurity Act, which maintains national cybersecurity in Singapore and protects organisations…

If you’re sitting at home right now, sheltering from the coronavirus pandemic – and there’s a good chance you are…

As the world “shelters in place” amid the COVID-19 crisis, some tech companies are stepping up and offering their products…
Due to the ongoing global pandemic, cyber criminals are taking advantage of unsuspecting users to breach their system. This might…

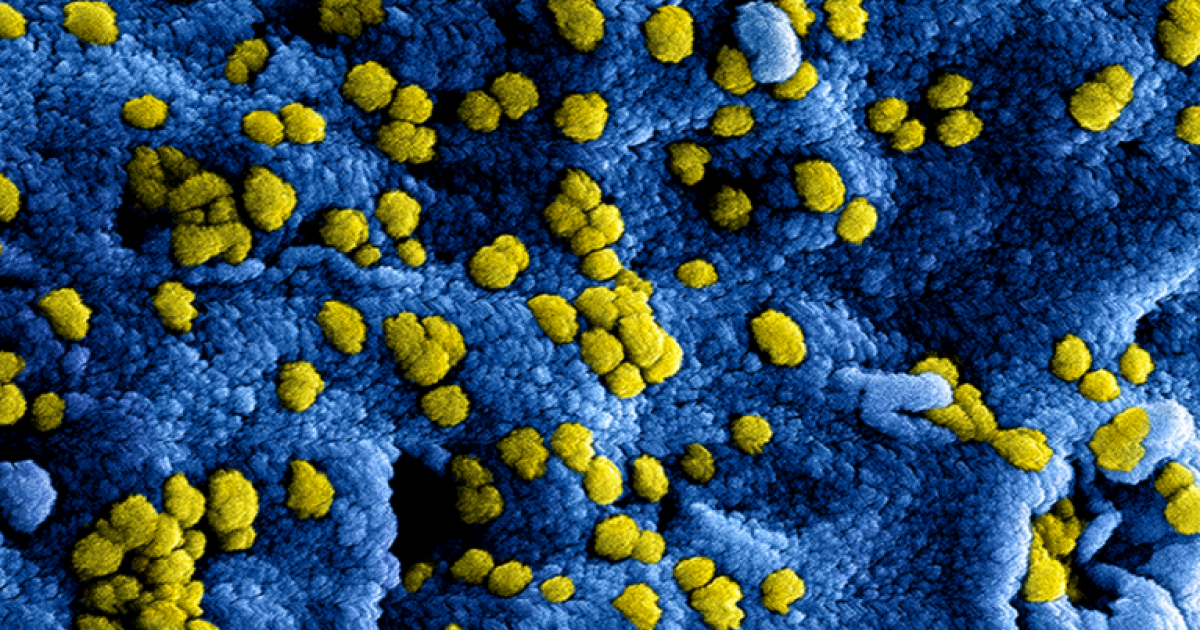
The ongoing worldwide outbreak of coronavirus disease (COVID-19), which originated in Wuhan, China, in December 2019, continues to grab headlines….

As the COVID-19 coronavirus rattles industries, it’s more important than ever for IT leaders to ensure employees have the tools…
No more posts available. Thank you for scrolling this far.
No more posts available. Thank you for scrolling this far.