The Future of Cyber Security in Kenya
Kenya has been dubbed the Silicon Savannah, a term that has spearheaded startups and investments both locally and internationally. As…
Analytical stories of tech trends, products, services, moves and technologies including cloud computing, security, big data, analytics, internet of things, artificial intelligence, storage, blockchain

Kenya has been dubbed the Silicon Savannah, a term that has spearheaded startups and investments both locally and internationally. As…

Companies must be cautious to safely dispose of data-rich electronics, especially in this rapid pace of technological and digital change….

Multinational cyber security and defense company, Trend Micro, has a 30-year history and is on the verge of making Africa…

Australian telecommunications infrastructure equipment provider, NetCom Wireless has today added to its indusrial Internet of Things(IoT) portfolio, launching the first…
Traffic index report released by numbeo.com in 2017 revealed that on average, Nairobians spend 62.44 minutes in traffic every day, making…
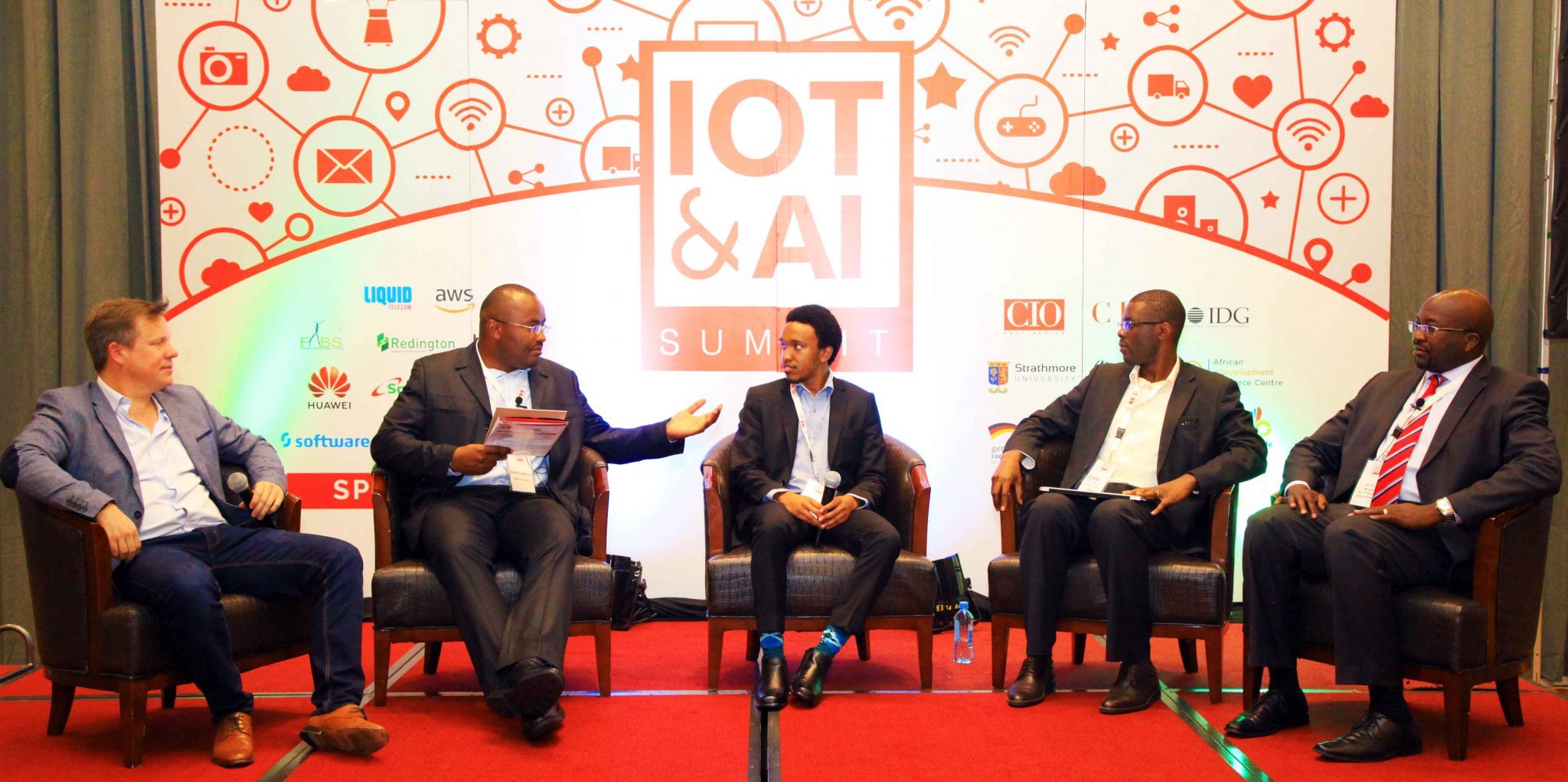
How individuals and corporate plug into the bigger picture of a better ecosystem in realizing smart cities is the responsibility…
Whether you rent or own, you want the best security camera system for keeping an eye on your home while…
Windows 10’s digital assistant is Cortana and, much like Siri, Google Assistant and Alexa, her usefulness depends on how much information…

NTT Security has released its 2018 Global Threat Intelligence Report (GTIR), which reveals ransomware detection increased globally by a staggering…

A former Federal Reserve executive believes it’s only a matter of time before central banks adopt a form of digital…
No more posts available. Thank you for scrolling this far.
No more posts available. Thank you for scrolling this far.