The Nairobi Innovation Week 2019- a Runaway success
The Nairobi Innovation week (NIW), an annual event on its fifth year running, was on Wednesday 12th June 2019, officially…
Analytical stories of tech trends, products, services, moves and technologies including cloud computing, security, big data, analytics, internet of things, artificial intelligence, storage, blockchain

The Nairobi Innovation week (NIW), an annual event on its fifth year running, was on Wednesday 12th June 2019, officially…
Big data is a big mystery these days. On one end, technology and its spectacular advancements has been touted as…

Microsoft has announced the scaling of its Cloud Accelerator Programme, an immersive 6-month programme designed to help women-led companies start and build…

The Trump administration did in 2018 March propose policy changes as part of the U.S government’s expanded ‘extreme vetting’ process for…

Cyber threat intelligence (CTI), an area of cybersecurity that focuses on the collection and analysis of information about current and potential…

The regional East Africa Fintech summit, an annual event on its second year running as hosted by CIO East Africa,…

In the last few years there have been a number of phrases and key words that have been floating around…
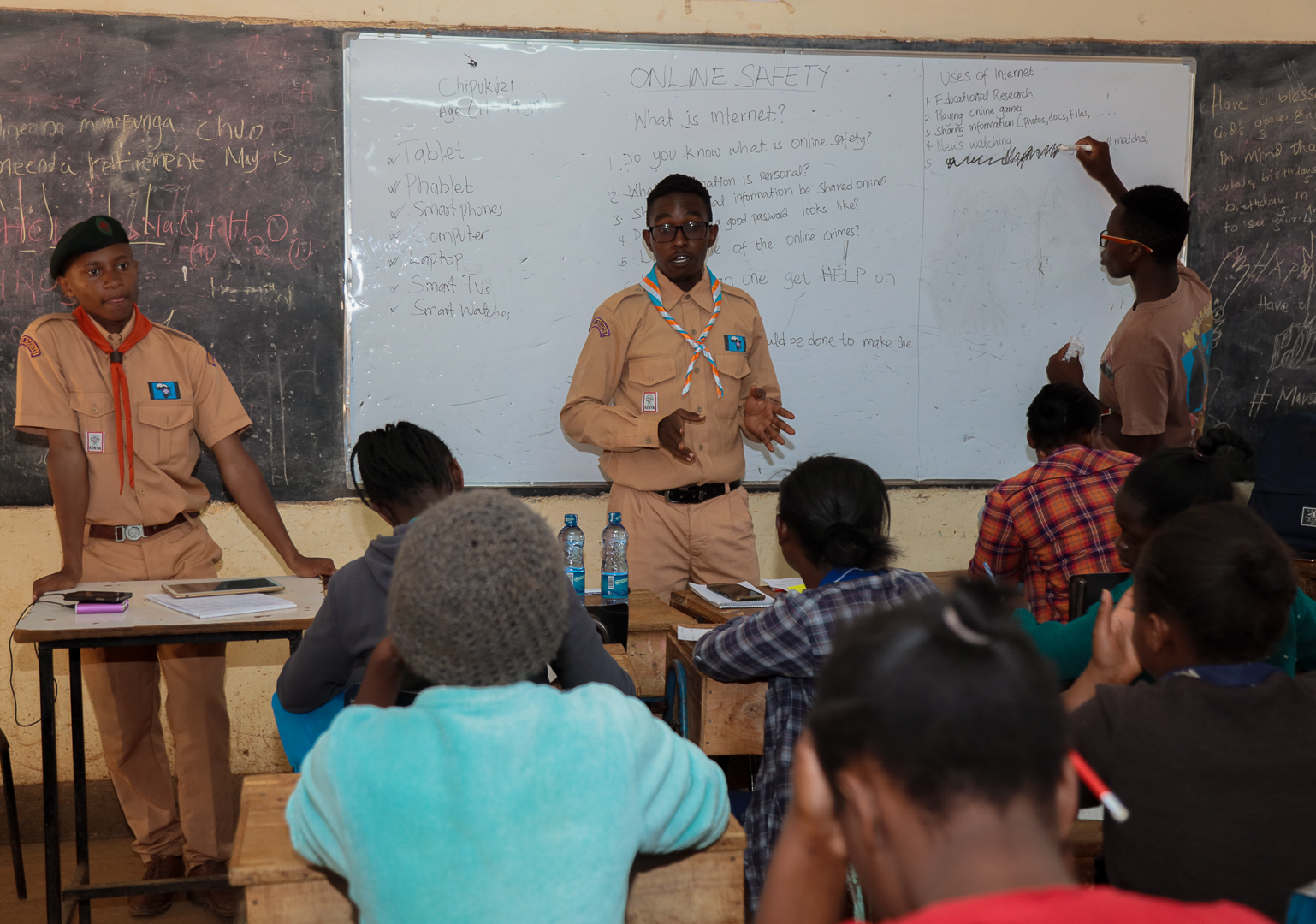
A Kenyan based NGO together with the Kenya Web Rangers have extended their online safety training to youth in Karuri…

Data was said to be the new oil that, bad as it sounds, can be used and/ or misused in…
Myths can be fun and entertaining when they involve the exploits of ancient gods and heroes. The amusement stops quickly,…
No more posts available. Thank you for scrolling this far.
No more posts available. Thank you for scrolling this far.