UCC to detect fake phones in Uganda
The Uganda Communications Commission (UCC), through its Executive Director Mr Godfrey Mutabazi, has confirmed the installation of equipment to detect…
Analytical stories of tech trends, products, services, moves and technologies including cloud computing, security, big data, analytics, internet of things, artificial intelligence, storage, blockchain

The Uganda Communications Commission (UCC), through its Executive Director Mr Godfrey Mutabazi, has confirmed the installation of equipment to detect…

The Kenya information and Communications (Amendment) Bill 2019, in seeking to regulate social media usage in the country, has proposed more…

Kaspersky has once again discovered a new malware that hijacks victims’ interaction with HTTPS web pages via patching the pseudo…

The Commonwealth has launched a regenerative climate change model that marries the ancient wisdom of indigenous groups with emerging innovations,…

The European Union court recently ruled against facebook, forcing it to globally delete illegal content form individual posts just a…

Opera Mini browser recently launched an accelerated offline file transfer platform that is made possible through a direct Wi-Fi connection…
Leading local value-added ICT distributor, Axiz, has cleaned up at the 2019 CONTEXT ChannelWatch Awards, winning in three categories –…

Kaspersky recently conducted an overview of smart building threats and reported that almost two in ten (26.5%) computers used to…
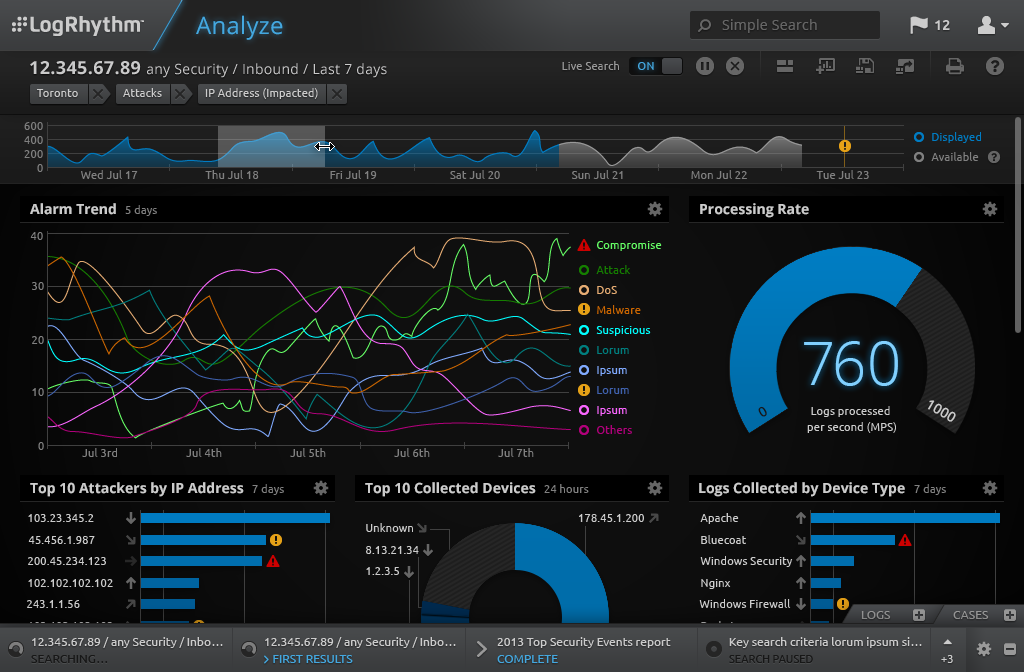
Historically, organisations have paid more as data ingestion increased. While others in the industry have previously claimed to support unlimited…

ThreatQuotient has announced that it shall be making its first appearance at GITEX Technology Week this year. A believer in threat…
No more posts available. Thank you for scrolling this far.
No more posts available. Thank you for scrolling this far.