What Are The Insurance Trends of 2019?
You know how there is an app for almost anything these days? Have you ever wished you could say…
Analytical stories of tech trends, products, services, moves and technologies including cloud computing, security, big data, analytics, internet of things, artificial intelligence, storage, blockchain

You know how there is an app for almost anything these days? Have you ever wished you could say…
With 5G poised to become widely available across the globe, enterprise organizations need to seriously consider the security implications of…

High-profile breaches have sparked interest in an emerging class of security software. The technology, named cloud security posture management (CSPM),…

Every technology organization today seems to practice the agile methodology for software development, or a version of it. Or at…

Safaricom recently penned a strategic agreement with Amazon Web Services (AWS), to see the Telco become a reseller of AWS…

Something is rotten in the state of Denmark—in all of Europe actually—and Amazon has been tight-lipped about it. It seems…
There’s no shortage of promising new technologies. The challenge lies in pinpointing the specific tools that have the potential to…

Kaspersky has yet again proven a ‘giant in the game of malware protection’ as by a 2019 report that lists…
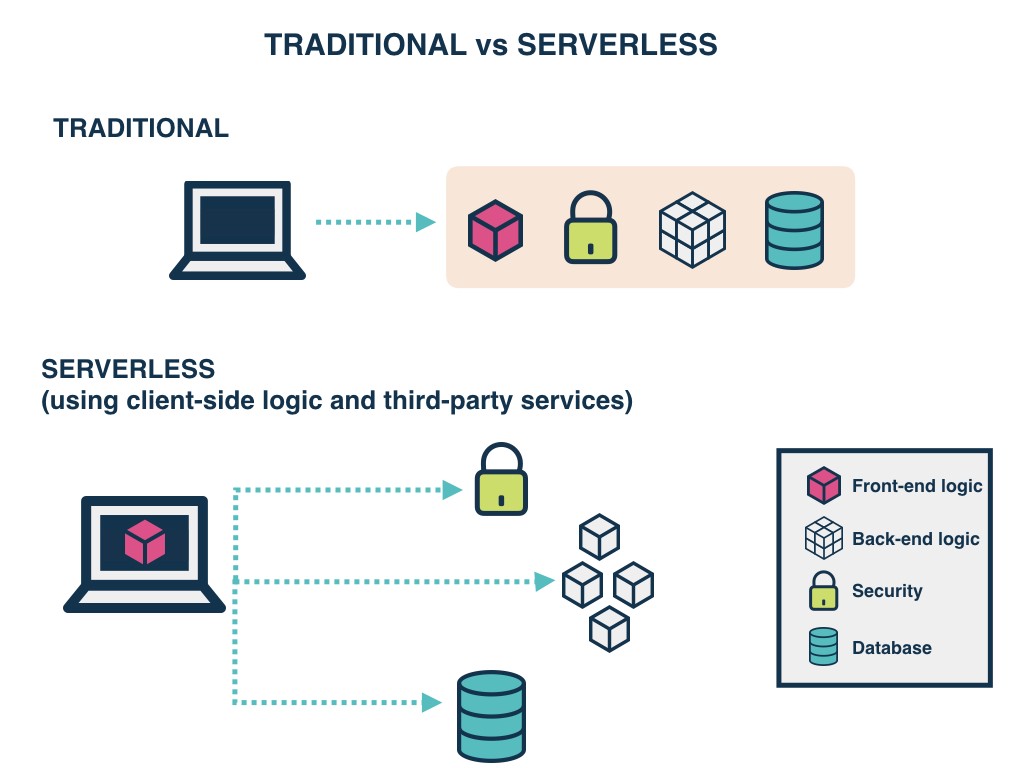
Serverless services are everywhere. The driving force behind an evolution towards a new way of programming, serverless offerings come in…

DATA. Your business and computers are full of it. While much of that data is useless to anyone else, every…
No more posts available. Thank you for scrolling this far.
No more posts available. Thank you for scrolling this far.