Is Catastrophic Forgetting The Reality of AI In Cybersecurity?
There is a lot of hype about the use of artificial intelligence (AI) in cybersecurity. The truth is that the…
Analytical stories of tech trends, products, services, moves and technologies including cloud computing, security, big data, analytics, internet of things, artificial intelligence, storage, blockchain

There is a lot of hype about the use of artificial intelligence (AI) in cybersecurity. The truth is that the…

The subject ‘data privacy, processing, and regulation’ is a famous one right now in Kenya, just months after the country…
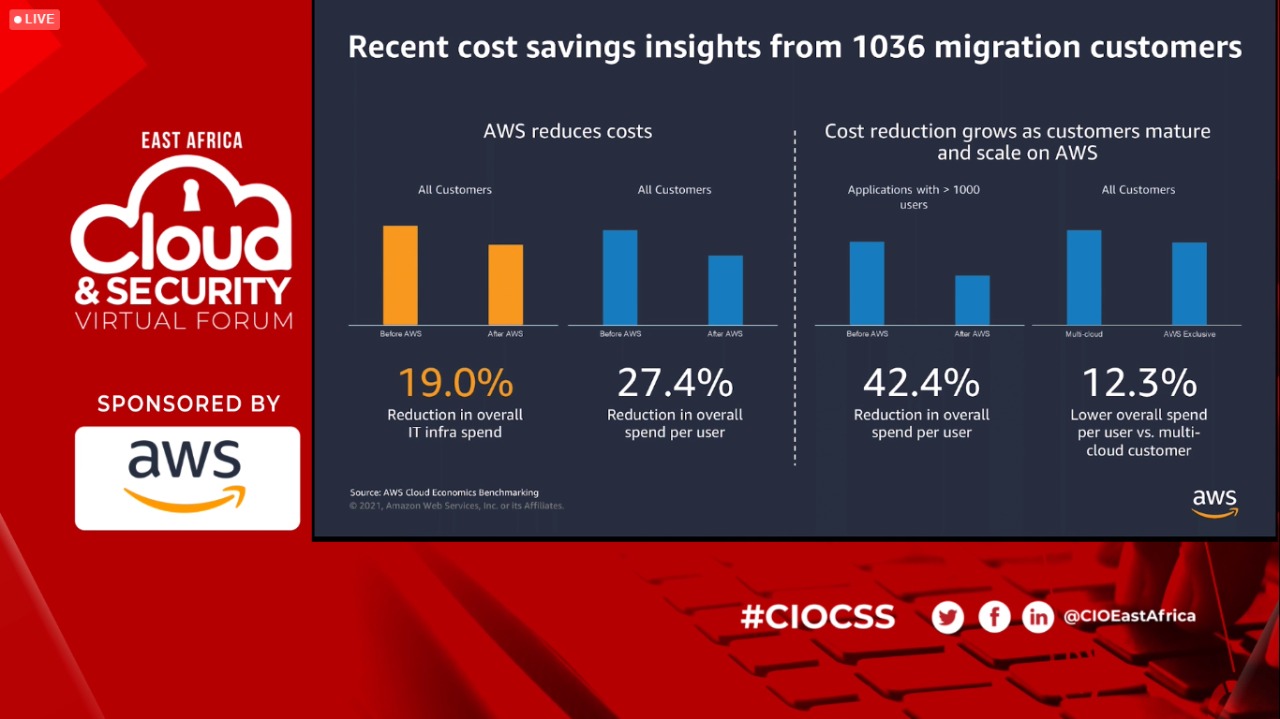
Amazon Web Services offers flexible, reliable, scalable, easy-to-use, and cost-effective cloud computing solutions and is considered the most simplistic form…

After the Microsoft Exchange vulnerabilities were reported and the out-of-band release of security patches on 2 March, security researchers started…

Checkpoint together with her partner DGIT has penned a sponsorship deal towards the forthcoming East Africa Cloud and Cybersecurity Summit…

Sophos has uncovered how attack code behaves while hiding in memory and built protection against it in a discovery bid…

Following Microsoft news on Hafnium, Sophos has been closely monitoring the issue and is providing regular advice on how organizations…

Accelerated digitisation is becoming the norm of the day in such unprecedented times. Kenya, and East Africa as a whole,…
Kaspersky researchers have identified a new, previously unknown, campaign from Lazarus, a highly prolific advanced threat actor active since at…

Siemon is urging manufacturers, producers, and other commercial organisations to maximise the potential of the industrial internet of things (IIoT)….
No more posts available. Thank you for scrolling this far.
No more posts available. Thank you for scrolling this far.