What the new Cisco-certification requirements means for you
Cisco’s network certification lineup has undergone a major overhaul. Starting today, the company has added a new coding-focused track to its…

Cisco’s network certification lineup has undergone a major overhaul. Starting today, the company has added a new coding-focused track to its…

The high demand for software developers has programming talent in short supply. And yet the seemingly insatiable need for new…
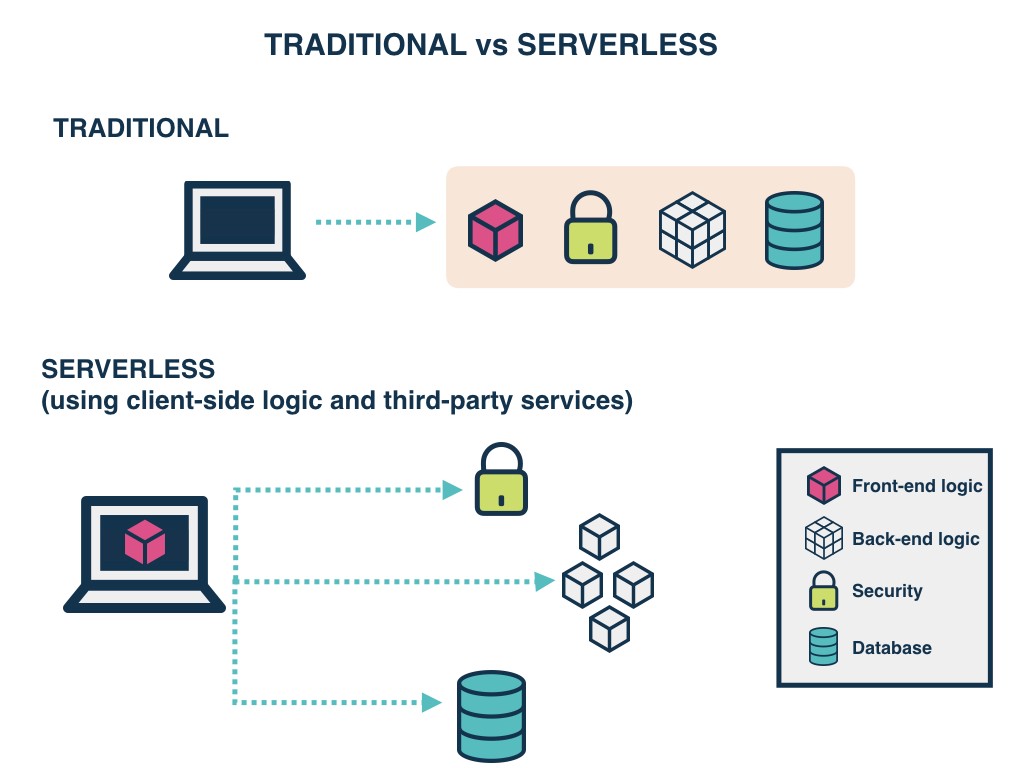
Serverless services are everywhere. The driving force behind an evolution towards a new way of programming, serverless offerings come in…

Few roles afford IT leaders the opportunity to double as both a strategic advisor to the CIO and as the…

DATA. Your business and computers are full of it. While much of that data is useless to anyone else, every…

History of ransomware Ransomware, a type of malware that holds data for ransom, has been around for years. In 1991,…
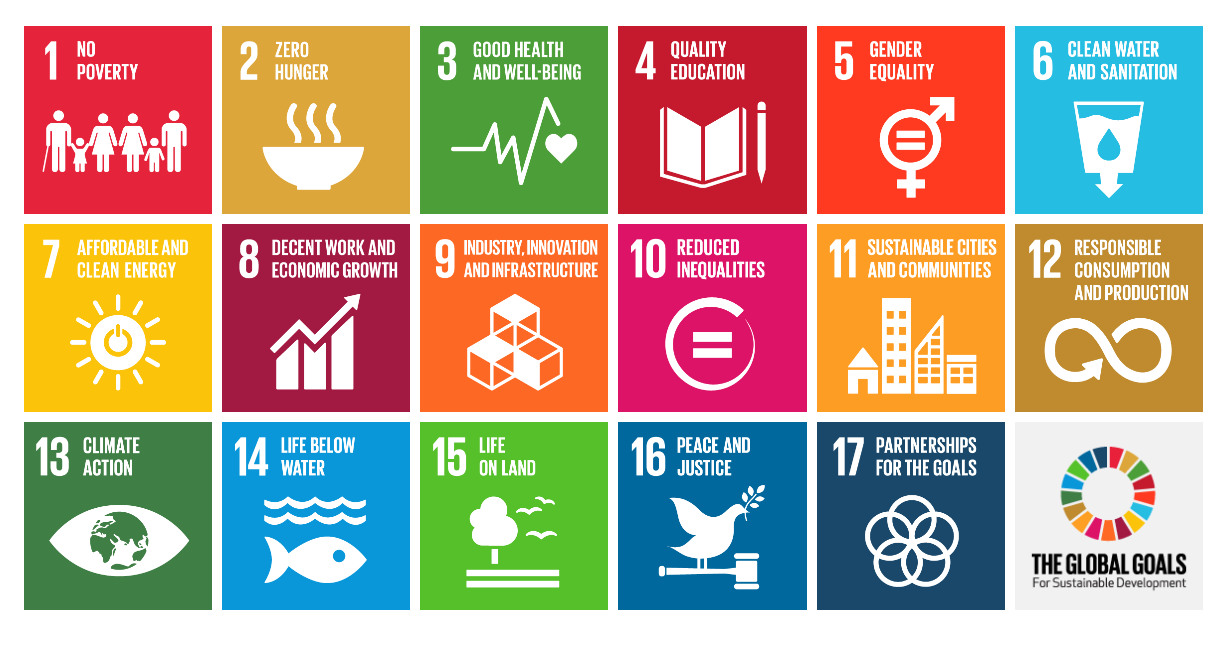
There is only one road left to achieving the Sustainable Development Goals (SDGs) set for Africa for 2030 and that’s…

Catholic Relief Services (CRS) has a mission to provide humanitarian relief to people in the developing world. Since 2016, it…

You leave kerosene-soaked rags all around your house. You chain smoke. One day, while relaxing in front of an episode…

While the Internet of Things (IoT) may still be an emerging technology, it is difficult to dispute that it has…
No more posts available. Thank you for scrolling this far.
No more posts available. Thank you for scrolling this far.