Ministry of Works Unveils Online Tool To Improve Transparency In Public Infrastructure
Uganda’s Ministry of Works and Transport in partnership with CoSt, a UK based Charity Organization, has developed an Online Infrastructure…
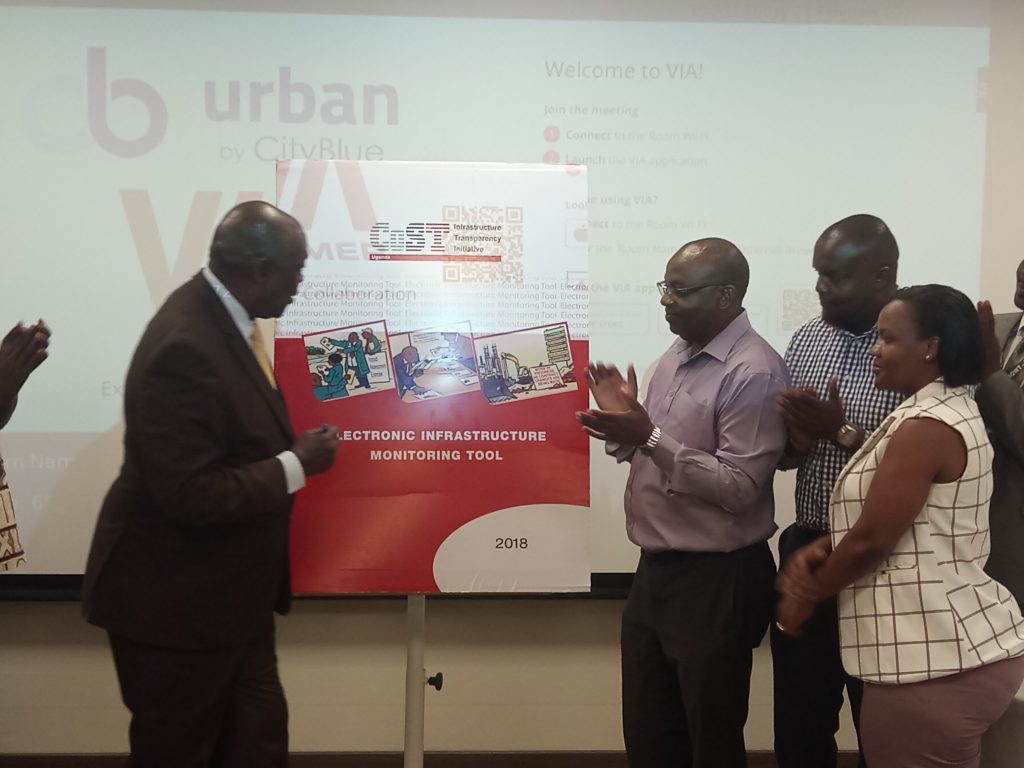
Uganda’s Ministry of Works and Transport in partnership with CoSt, a UK based Charity Organization, has developed an Online Infrastructure…

Stanbic Bank Uganda Chief Executive, Patrick Mweheire appointed Regional Chief Executive, Standard Bank Group, as Anne Juuko steps in his…

Airtel Uganda Managing Mr. V.G. Somasekhar, aka Soma, has relocated to India Airtel Group, according to information availed to…
There are two forms of Influencer marketing you can choose from for your Instagram marketing efforts. These are micro…

AVEVA and Axonify jointly deliver first AI-enabled Microlearning Solution to Industry 4.0 Customers. AVEVA, a global leader in engineering and…
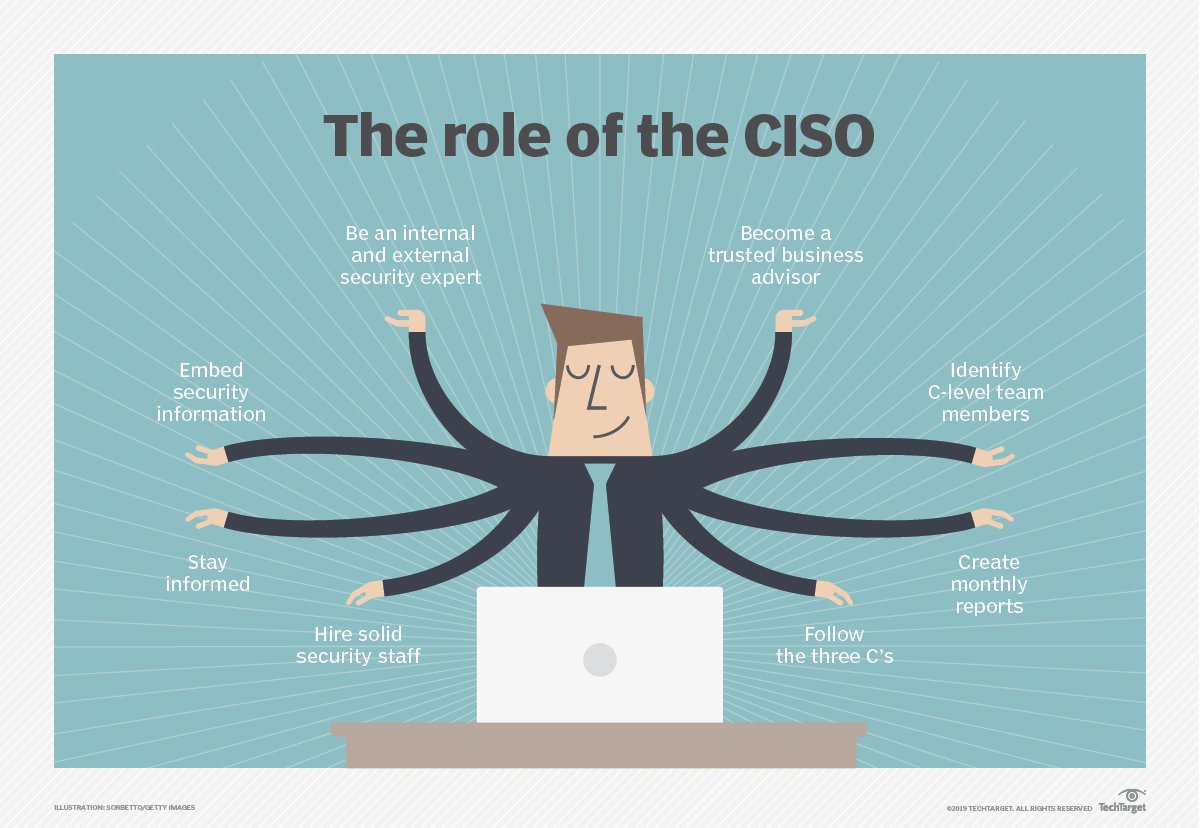
The scramble to enable remote workers changes security strategies, priorities, and workflows for 2020. According to ESG research, 62% of…

Nigerian serial tech entrepreneur and software developer, Chidi Nwaogu, has just won the Migration Entrepreneurship Prize. Nigerian techpreneur Chidi…
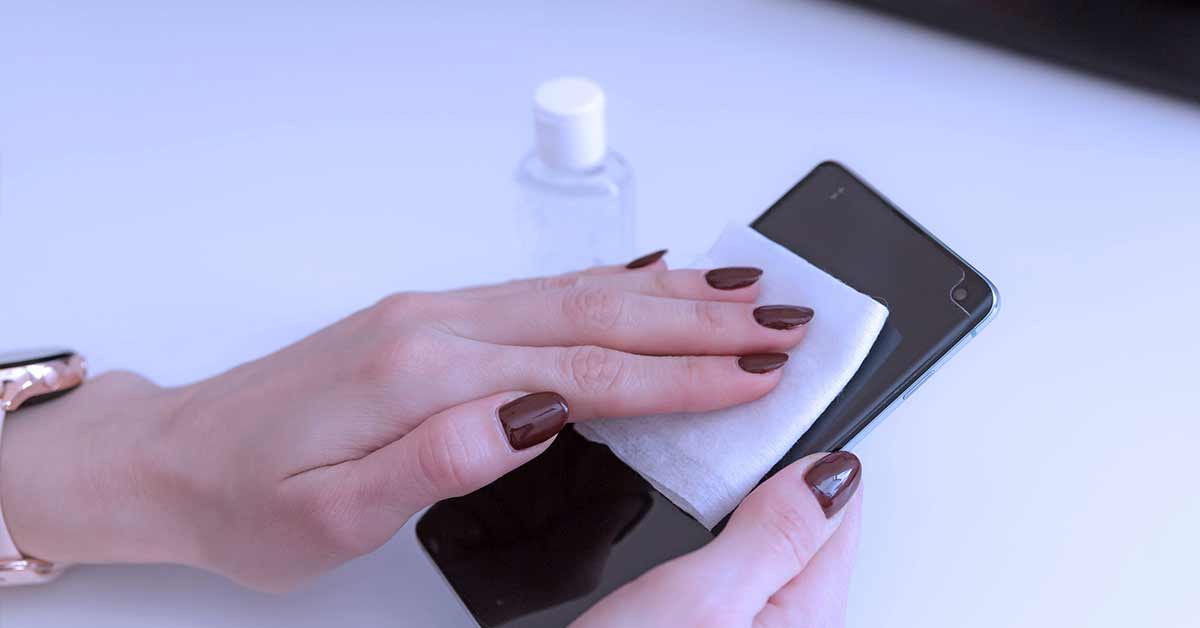
The outbreak of COVID-19 has encouraged consumers everywhere to be a little more vigilant and conscious of how exposed their…

The coronavirus holds no quarter for humans, with its merciless march punishing businesses worldwide. Desperate to flatten the COVID-19 curve,…

When analysts began forecasting the challenges that CIOs would face in 2020, uncertainty became a common theme. But few would…
No more posts available. Thank you for scrolling this far.
No more posts available. Thank you for scrolling this far.