Liquid Telecom launches 5G in South Africa
Liquid Telecom is set to launch the first 5G wholesale roaming service in South Africa to allow businesses harness new…
Analytical stories of tech trends, products, services, moves and technologies including cloud computing, security, big data, analytics, internet of things, artificial intelligence, storage, blockchain

Liquid Telecom is set to launch the first 5G wholesale roaming service in South Africa to allow businesses harness new…

As a consumer, I enjoy the fact that many services are now available for us to use at any time…

Although the snooze button is probably the most commonly used button on an alarm clock, even a simple AlarmClock class needs a…

We’re only a few weeks into the new year, but already we’re seeing signs that automated machine learning modeling, sometimes…

More than any other industry, technology suffers from misplaced industry jargon. CIOs are battered by consultants hawking cure-all strategies and…
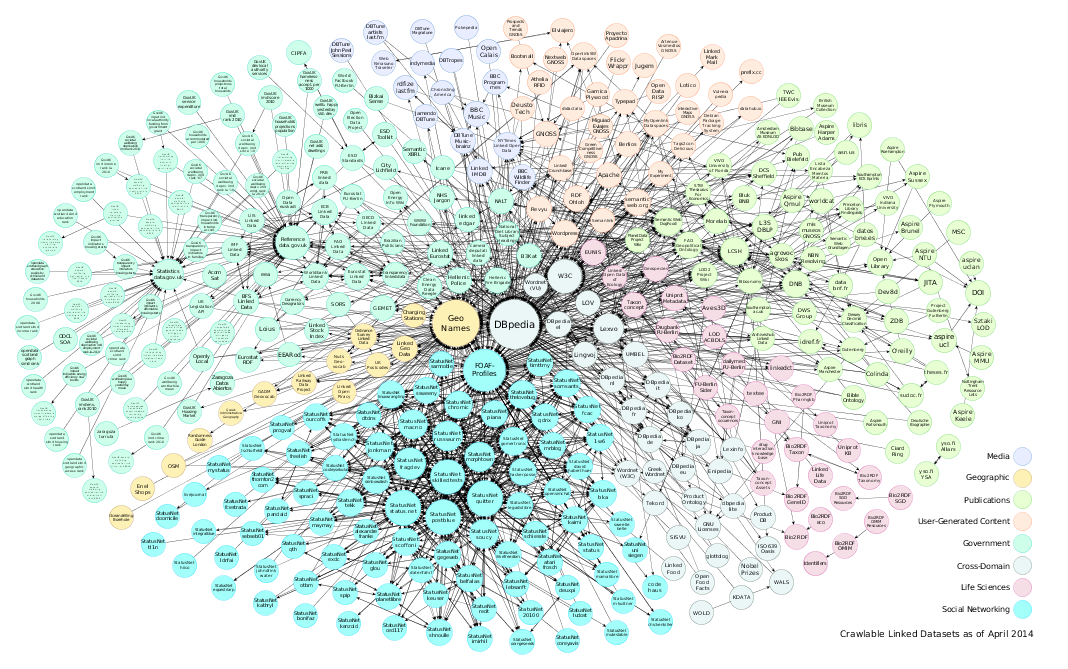
Relational databases, data lakes, and NoSQL data stores are powerful at inserting, updating, querying, searching, and processing data. But the…

First the good news: Microsoft planned to release a patch in January to disable insecure LDAP channel binding and LDAP…

Even in the high-touch field of healthcare, where human interactions remain core to the delivery of most services, IT exec…
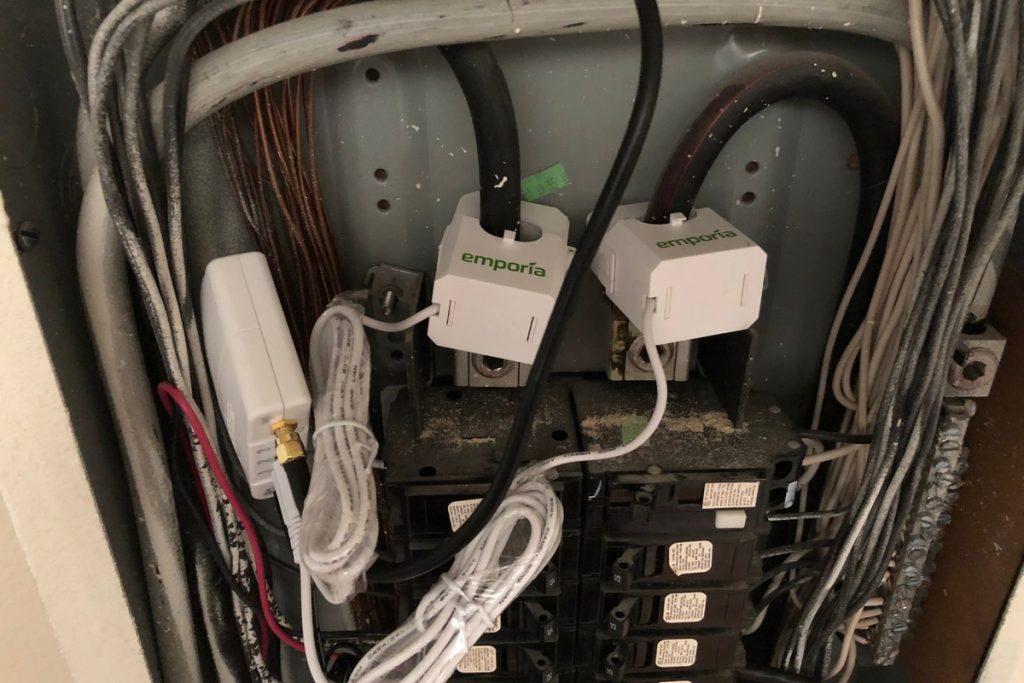
Even novices can use this system to easily get a grip on how much juice they’re using Want to know…

Imagine what you would have done differently in your network if you could have just seen a few years into…
No more posts available. Thank you for scrolling this far.
No more posts available. Thank you for scrolling this far.